Aktuelles

Finanzen
“Geldanlage ist ein Thema, mit dem man nicht zu früh starten kann!” Diese Binsenweisheit hat vermutlich jeder schon einmal gehört. Aber wenn man dann irgendwann auf sein Konto schaut, gerade im jungen Alter, muss man [...]

OpenNebula Workshop
Online & Technik
In einem OpenNebula Workshop lernen Teilnehmer, wie sie die Open-Source-Cloud-Computing-Plattform OpenNebula einrichten, verwalten und nutzen können. OpenNebula wird für die Implementierung von privaten und hybriden Clouds verwendet und bietet eine flexible, skalierbare und benutzerfreundliche Lösung [...]
Freizeit
Singapur – die Stadt im Garten
In der dicht bevölkerten Landschaft der globalen Metropolen erhebt sich ein leuchtendes Beispiel für Harmonie zwischen Mensch und Natur: Singapur, die „Stadt im Garten“. Dieser kleinen, doch imposanten Inselnation ist es gelungen, eine Vision zu [...]
Freizeit
Passives Einkommen Kickstart
Geld verdienen, ohne dafür einen Finger krumm machen zu müssen. Das sogenannte „passive Einkommen“ klingt sehr verlockend und ist für jeden von uns erreichbar. Doch mit welchen Methoden und Strategien dies erschaffen wird, variiert deutlich. [...]
Freizeit
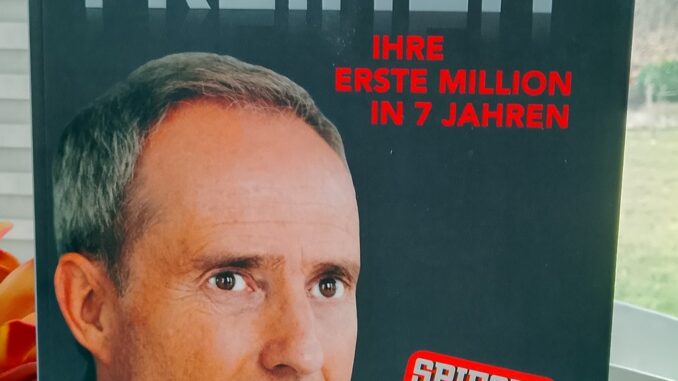
Der Weg zur finanziellen Freiheit
Heute schreiben wir über keinen Geringeren als Bodo Schäfer. Ein Finanzcoach und Bestseller-Autor. Herr Schäfer hat es sich zur Aufgabe gemacht, möglichst viele Menschen in finanziellen Belangen zu bilden. Erfolgreich wurde er in erster Linie [...]